Your complete procurement management solution for large, complex infrastructure projects
Your complete procurement management solution for large, complex infrastructure projects
The only software solution purpose-built to run large, complex, high-value procurement
Procurement processes have grown more complex, but the systems for dealing with this risk haven't changed.
At Ansarada, we provide unmatched order to your project procurement chaos.
The trusted platform used to procure over $1 trillion worth of complex infrastructure projects
From shipping ports, airports, roads, rail, stadiums, hospitals to energy infrastructure and broader precinct renewals.

Ease of access
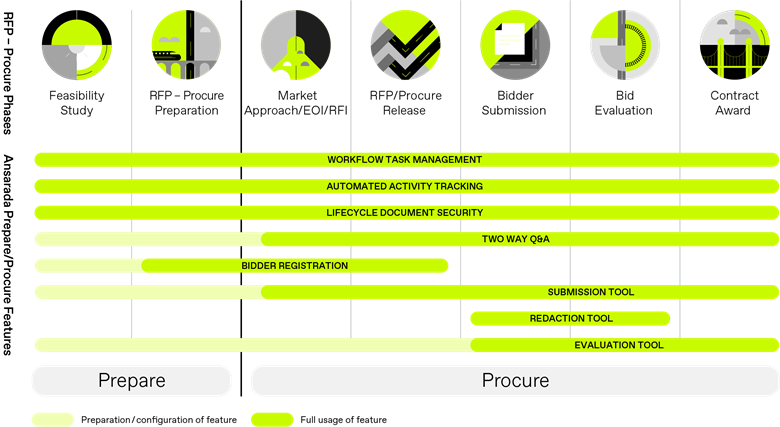
Intuitive and accessible for all users, with zero plugins or software to install. Setup takes a few hours - not weeks

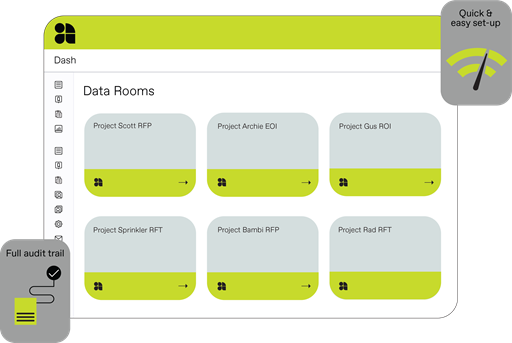
2-way RFI / Q&A system
Purpose-built two-way Q&A and collaborative tools, including robust approval workflows

Secure, tracked submissions
Integrated, highly secure ‘locked box’, multi-window submission tool

AI Bulk Redaction tool
Built-in software to create multiple redacted versions of bidder submissions

Evaluation tool
Integrated functionality manages the entire evaluation process securely from start to finish

Probity automated
Intelligent reporting and comprehensive audit trails are available on demand

Stay protected
Benefit from the highest levels of document security and tracking, including features like remote file kill-switch

24/7/365 support
Best-in-class training and help from the Ansarada team, who have experience running the world’s largest infrastructure projects
This is Procure
Helping you run large, complex, high-value infrastructure procurement
Your definitive procurement checklist
The only procurement lifecycle management technology
Less procurement risk. More progress.
What does order look like in a complex procurement process?
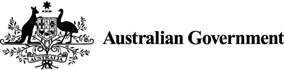
From preparation, to managing bidders' access, two-way Q&A, and the secure disclosure, submission, evaluation and award process, our platform has you - and your project - covered.
Set up a fair and equitable process in minutes
Automate processes and use granular access and permission settings to enable large numbers of users, documents and requirements with the relevant levels of confidentiality. Get proof of disclosure records and comprehensive reports to prove probity in a single click. Track document views, searches, downloads and printing – both internal and external.
Keep Q&A contained and tracked
Two-way Q&A functionality keeps the entire process within the platform, with both sides able to ask and answer questions from a single role. Answers are disclosed to a single party, or many parties – without revealing identities – and RFI workflows are automated to ensure procurement compliance. Auditors receive a single source of information exchange to review.
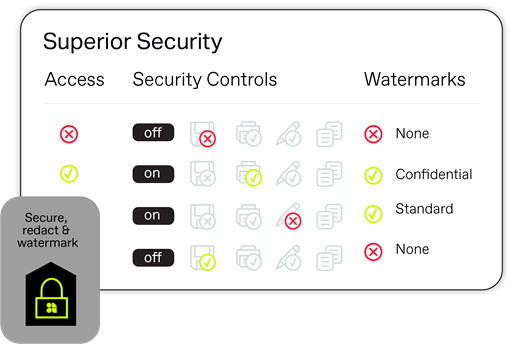
Secure by design
Track usage and take back documents whenever you like, even after they’ve been saved and downloaded. Protocols are verified in real-time, so revoking access is instant. For an extra level of protection on your high priority material, take advantage of print, save, edit and watermark restrictions.

Global document storage
In keeping with strict and fastchanging data privacy laws, when creating a new Procure Room, we’re offering users a choice for where their at-rest documentation is stored. Full compliance with the laws of your region, plus the expertise and reach of a global company. The best of both worlds.
Get the Playbooks for smoother procurement processes
Catch up on past webinars that deep-dive on a feature

We use systems like Ansarada where it’s all controlled and managed. Once it’s set up and it’s operating, you can’t send the wrong information to the wrong person.John McLuckie, Valorem Advisory
Trusted by leaders globally
Transurban's success story on Ansarada
Sean Mallipudi is the Director, Procurement & Corporate Services at Transurban in Greater Washington, United States. Sean uses Ansarada for all Infrastructure Procurement projects.